
Agile Working introduces additional security threat
Agile working, as a form of mobile working, introduces additional security threats to those arising from office based working.A number of recent surveys have highlighted the security risks of Agile Working as being one of the greatest concerns for businesses adopting agile working especially for employees using personal devices for work. For example a YouGov survey revealed that whilst 47% of all UK adults now use their personal smartphone, laptop or tablet computer for work purposes, less than three in ten are provided with security guidance. It is essential that the security issues of Agile Working are addressed. A particular concern is data; whilst much of the data will be held on corporate servers a significant amount of business data, often sensitive in nature, could be held on mobile devices, where corporate and private data may co-exist for staff adopting a work-life integration workstyle. This section discusses the security risks from Agile Working and how they can be mitigated. If data is not stored on the corporate network, at best it will be backed up through the agile worker’s personal backup facilities, and at worst it will not be backed up at all. The organisation could lose sight and control of its data if only stored locally on the BYOD device. Corporate data is at risk from the unauthorised access through mobile devices.
Mitigating data loss from Agile Working
The essential precautions for addressing the risks of Agile Working are to ensure the safety and security of this data include:
- Encryption which protects information by scrambling the original message with a very large digital key. The computer receiving the message knows the key and so is able to decrypt the original message. As long as the secret key is only known by trusted parties, the cypher-text is very hard to de-crypt or un-encrypt by external parties. Having encryption enabled means that if an agile worker loses a mobile device, it is highly unlikely that anyone who finds it can get any information from it.
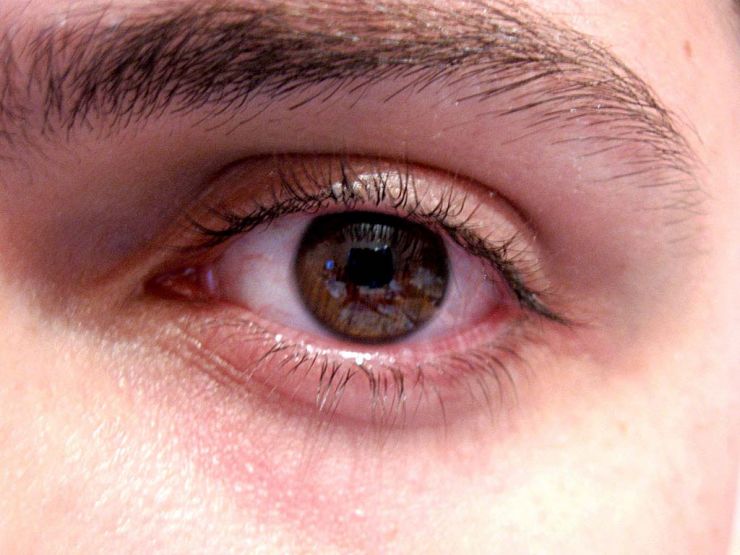
Retina scans can be used for authentication
- Authentication is a way of ensuring that somebody is who they say they are. Typically it is a combination of something the agile worker knows (such as a password or PIN code), something the agile worker has (such as a security device, or token), or a personal attribute concerning the agile worker (technology that makes use of fingerprint recognition, retina scans, or facial recognition). With these authentication factors remotely held data cannot be accessed from lost or stolen devices.
- Remote Wipe is a feature that allows IT support teams to remotely delete all information held on a device if the agile worker has reported the device as lost or stolen. For many organisations having information stored locally on a device is only acceptable if that device has a remote wipe capability. This has serious implications if agile workers choose to keep personal photos, data, or music on their devices and have not backed them up elsewhere.
- Device lock-down allows IT support teams to decide what subsets of features are available on a device to an agile worker. For example an agile worker may be allowed to use all installed applications, but may not be allowed to install any new ones, or may be allowed to use business applications, but not play games or use social media applications.
- Viruses and malicious software (malware) are also risks that need to be addressed. Most Anti-Virus vendors now offer solutions that include products for laptops, mobile devices and tablets.
Agile Working policy
Another way of addressing the security risks of Agile Working is to ensure that employees are aware of their responsibilities. An acceptable use policy should clearly define the terms and conditions agile workers must agree to before they are allowed to connect devices to the corporate network. The Information Commissioner’s Office (ICO) provides guidance on the use of mobile devices in a manner that complies with the Data Protection Act. An agile working policy should require agile workers who use mobile devices to install various security tools on them and change security configurations. Manually entering security configuration settings and selecting patches is highly subject to human error and in practice requires oversight and assistance from the IT team. A more comprehensive and systematic, mobile device security solution is provided by technologies such as enterprise Mobile Device Management (MDM) and Network Access Control (NAC). These technologies can be used to manage smartphones, tablets, and notebooks providing a single solution for multiple platforms. For example an MDM can:
- Lock the device remotely, or set/reset a pin code;
- Locate the device remotely;
- Wipe the device remotely;
- Restore settings and preferences to a new device;
- Restore Wi-Fi and VPN (Virtual Private Network) settings to a new device;
- Restore previously installed applications to a new device;
- Restrict the capability of devices
Data-Centric security approach to address security risks of Agile Working

The MDM approach can be regarded as device-centric security. In a data-centric security approach, apps and data can be partitioned, or apps can operate around the data. Personal and corporate data types can be kept separate. Corporate apps with sensitive data can be ‘sandboxed’ off from other content in an encrypted container. If an agile worker downloads an app that contains malware, the malware cannot access the data inside the container. Many IT teams are moving to a data-centric model for other aspects of enterprise infrastructure—data loss prevention, data centres, database monitoring. Data-centric security provides agile workers with device choice and privacy, while enabling IT with manageable policies and reliable control over sensitive data. In practice, groups of agile workers will have very differing demands. Some will need high levels security and control at all times, while others may need only moderate or low levels. Putting a flexible infrastructure in place can help address this reality by tailoring security to each group’s working model.

